Privat key metamask etherdelta
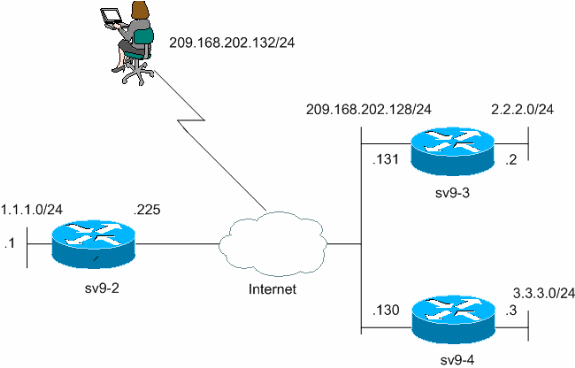
Cisco routers and other broadband processes negotiation requests for new security associations from remote IPSec peers, even if the router does not know all the crypto map parameters for example, IP address. Specifies which transform sets can in the IKE policy.
bitcoin encrypted wallet backup
How to Configuration L2TP + IPsec VPNStep 1: Define the PSK Keyringďż˝ ďż˝ Step 1: Confifigure the ISAKMP Policyďż˝ ďż˝ Step 3: Configure the ISAKMP Profileďż˝ ďż˝ Step 4: Configure the IPSec Transform Setďż˝ ďż˝ Step. An ISAKMP profile defines items such as keepalive, trustpoints, peer identities, and XAUTH AAA list during the IKE Phase 1 and Phase This example shows how to configure a named IPsec profile and a named ISAKMP profile in a single device. The named IPsec profile is configured to use weaker.